The PPPoE is the standard configuration to enable most consumer internet connections networks. It is the favored method because it provides ease of management with respect to the account, bandwidth, etc.
The PPP is a legacy serial link technology that helps to connect between the WAN links. However, PPP doesn’t support natively on the ethernet; hence we use PPP over ethernet called PPPoE.
How to configure PPPoE with VLAN on Fortigate?
Some ISP’s use PPPoE with VLAN tagged, and some use without VLAN. When you have VLAN tagged, there are two ways you can configure the fortigate firewall for PPPoE. By default, fortigate does support VLAN tagging on the WAN interface, so you can create a VLAN interface on the fortigate firewall and then configure PPPoE.
You can also get rid of the VLAN tagging by using a layer 2 switch at the edge of the network if you face some challenges configuring the PPPoE with the VLAN interface. Connects ISP link to the internet service provider, speak to the ISP support, and get the VLAN ID. Configure the layer2 VLAN on the switch. And configure the internet port connected to the switch as VLAN tagged, and configure the port towards the fortigate firewall as an access port (untagged port ) in the same VLAN. After which, you need to configure the PPPoE without worrying about the VLAN tagging on the fortigate WAN interface.
You can learn more about VLAN configuration on fortigate here.
In this blog article, we will look at PPPoE configuration on fortigate firewall without the VLAN, and later we will test with the VLAN.
Why can’t I connect to the PPPoE network on fortigate?
When you cannot configure the fortigate firewall for PPPoE, you first need to get the configuration details from the internet service provider. And verify the following,
- Have you entered the correct credentials.
- If the ISP uses the VLAN, has it been configured correctly on the fortigate firewall?
- Finally, the ISP finally cleared the MAC address for the old device.
Before deploying the FortiGate firewall in the network, you might have used another router or firewall with a PPPoE configuration. Usually, the internet service provider will cache the MAC address of the respective router’s WAN interface in this kind of setup. So before you deploy the fortigate firewall for PPPoE, you need to call the ISP and ask them to clear the MAC address after unplugging the old router or firewall. And then proceed with the fortigate firewall configuration. After you have configured the fortigate firewall, your ISP will continue to cache the new MAC address of the fortigate firewall. You need to keep in mind that anytime you add new network devices to the PPPoE network.
Read also,
Build a FortiGate lab using GNS3 – Step by Step Guide.
How to Configure DMZ on the FortiGate Firewall? | Step by Step
How to Configure IPsec Site to Site VPN on FortiGate Firewall?
How to Configure FortiGate Port Forwarding?
How to Deploy FortiGate Firewall on AWS EC2?
Before you begin, you need to have;
- Working internet service over PPPoE.
- Get the credential and VLAN information.
- Fortigate firewall.
- Optional: Use a layer2 switch with VLAN tagging capability to remove the VLAN tagging on the fortigate PPPoE link.
Configure the LAN interface for managing the fortigate.
We will configure the LAN interface on the fortigate firewall with an IP address with HTTPS ping and SSH services enabled. That way, we can access the fortigate firewall web GUI and SSH to manage the firewall.
Power on the fortigate firewall and Console into it, and configure the LAN interface as below. We will configure the WAN link within the CLI itself, the reason we are configuring the LAN interface to manage the firewall GUI and SSH.
We are using 10.1.1.0/24 subnet, so based on your network, you may change that.
Config system interface
edit port2
set mode static
set ip 10.1.1.1/24
set role lan
set allowaccess https ping ssh
endConfigure the IP address from the same subnet, and Plugin the PC/Laptop to the LAN side of the fortigate firewall,
Configure FortiGate WAN interface with PPPoE without VLAN.
We have used port 2 for the LAN link, and we would use port 1 for the WAN link, so based on your setup, choose the ports.
Config system interface
edit port1
set role wan
set mode pppoe
set pppoe username yourusername
set pppoe password yourpassword
endThat’s it you have configured the WAN interface successfully.
I use a static IP address on my network, meaning the ISP will hardcode the static IP on my WAN interface. The only difference here is, when you have DHCP from ISP, after a certian time, the IP address will change. However, my IP address is permanent.
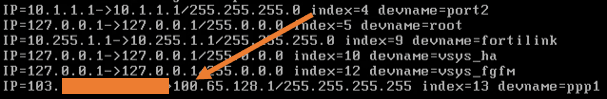
You can type diagnose IP address list. As you can see, port1 is configured as WAN, and it gets an IP address from the ISP.
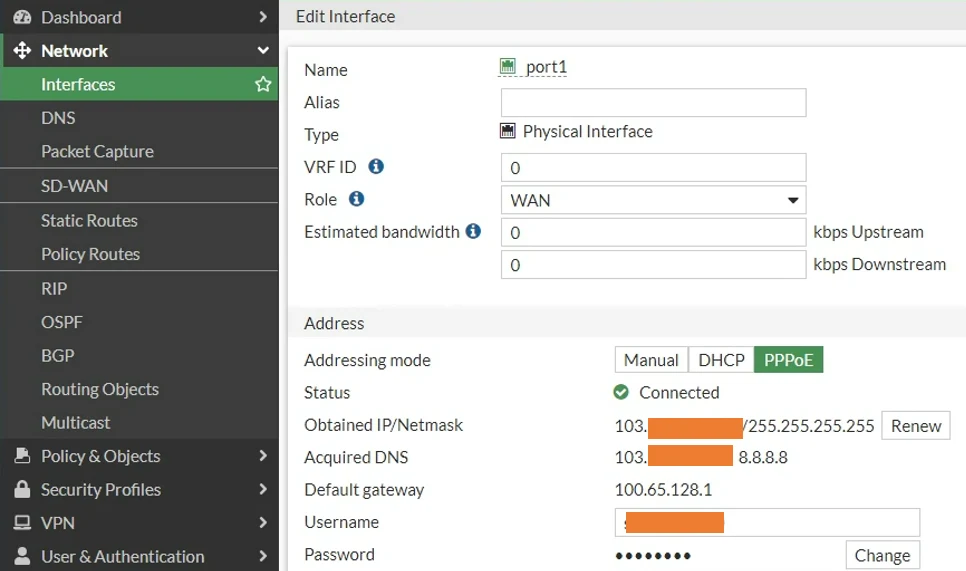
You can also see the same information from the web GUI of the firewall. Click on the interface and you should see the PPPoE configured with the IP address on port1.
You can now configure the static route and the security policies to allow the network traffic from the LAN to go out to the internet.
Configure the FortiGate WAN interface with PPPoE VLAN.
We looked at the configuration of the fortigate firewall pppoe interface without VLAN above, which was pretty easy. What if your ISP uses VLAN and you need to configure the WAN link as PPPoE VLAN?
Let’s take a look at that.
Create a VLAN interface for the ISP.
You need to speak to your ISP and get the VLAN ID they use for your network.
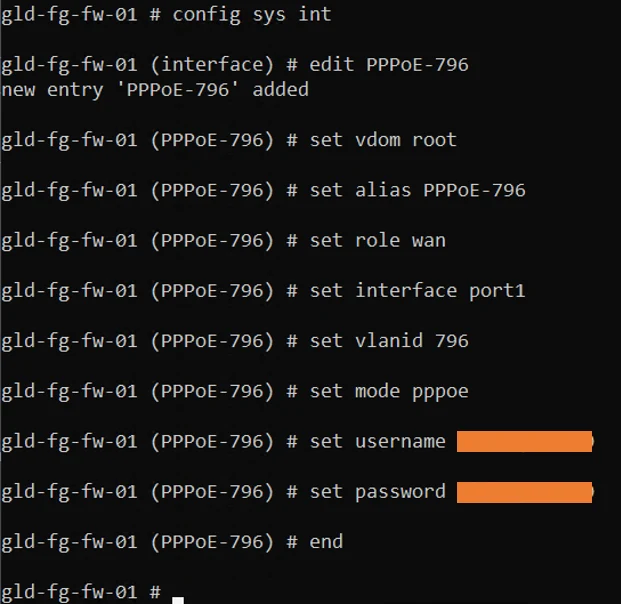
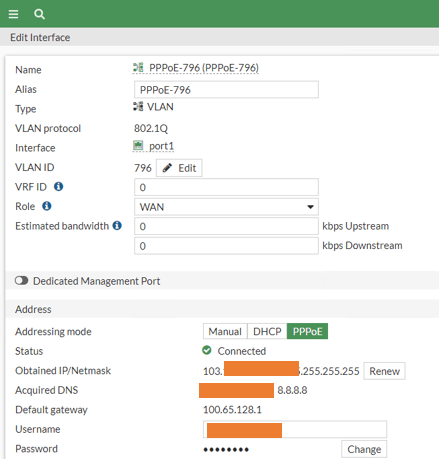
In this example, I will use VLAN 796, and the interface on which we will configure the VLAN is on port1.
It is assumed that you already have access to the fortigate CLI, be it through the LAN interface or via Console.
Config system interface
edit "PPPoE-796" #we are creating vlan interface, provide user friendly name.
Set vdom root
Set alias "PPPoE-796" # provide meaningful name here as well.
set role wan
set interface "port1" #Choosing the vlan physical interface
set vlanid 796 # setting the VLAN ID.
set mode pppoe # setting the mode on the VLAN interface.
set username yourusername
set password yourpassword
end.Below is the snippet of the configuration.
After a second or two, you will see the PPPoE connection gets established.
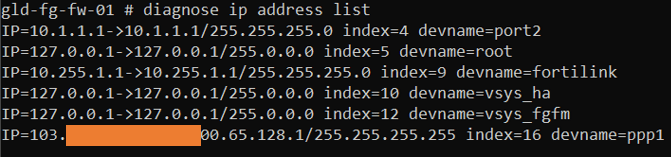
You can type the command diagnose ip address list
And you should see the IP address in there.
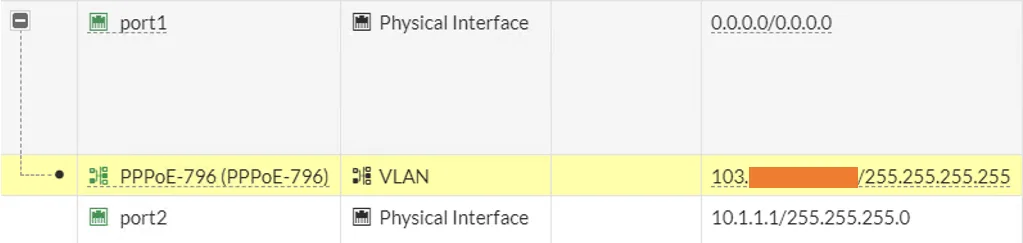
Login to the GUI and expand the WAN physical interface, and you can see the VLAN address is now configured with new public IP address.
You can double-click on the VLAN interface to see the configuration in detail.
For the LAN devices to access the internet, point the static route towards the VLAN interface, and create a security policy to allow the traffic from LAN to Outside.