When I started my Paloalto firewall journey, it wasn’t easy. I am from a network routing and switching background, and initially, when I had a chance to work with Palo alto firewall, I was a little hesitant.
Eventually, I set up the Palo alto firewall lab and started to practice. Slowly I began to get the hang of it. After many trials and errors in the Palo alto lab exercises, now I am more comfortable to work on it.
I hope my journey would inspire some of you out there to get started.
If there is a will, there is a way
unknown
We have configured the Palo alto lab in gns3 in our last blog. You may start there before we proceed with the Palo alto firewall basic configuration. how to set up and everything pretty much covered there.
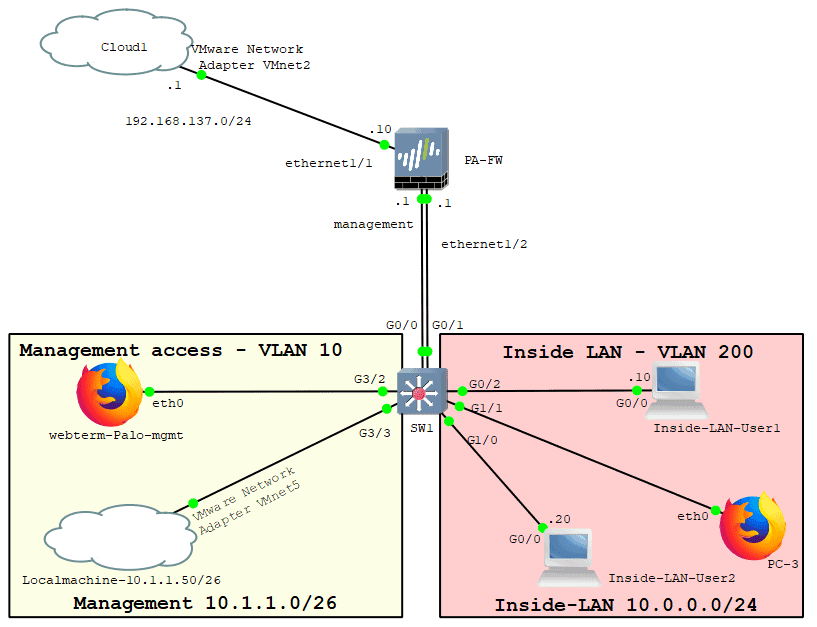
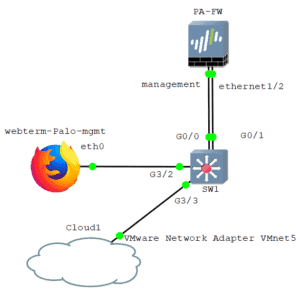
Below is the Palo alto lab topology that we will be working on. Again this is just a basic setup.
And this lab may feel long, but take one step at a time, and you should be good to go and one important thing, practice is the key.
How to allow internet access through firewall?
We will be connecting the Palo alto firewall to the Internet, and also connect the LAN users. After that, we would allow end-users to access the Internet via the Palo alto firewall using security and NAT policies.
Allowing internet access through a firewall is quite easy, controlling them is the tricky part. Since we are starting from scratch which including setting up the Palo alto firewall initial configurations, this guide seems quite long. But if your goal is to just allow the inside users to talk to the internet you just need to do step12 and 13 below.
- Configure the firewall management interface.
- Connect the switch to the Palo alto firewall.
- Connect management client to the switch.
How to connect your local machine to access Palo Alto GUI? - Configure the Outside interface.
- Create the outside zone.
- Configure the routing for the outside interface.
- Allow Ping to the Firewall outside interface.
- Configure the internal interface.
- Create the Inside zone for the Firewall.
- Add LAN users to the Network.
- Allow PING on the internal interface.
How do I connect my Palo Alto firewall to the Internet? - Configure security policies to allow inside to outside.
- Configure NAT on the Palo alto firewall.
1. Configure the firewall management interface.
I have already created a project called Palo alto lab firewall basic configuration.
Add the Firewall to the topology and Configure the management interface.
Make sure that you are using the network interface as e1000. If you have followed the guide on how to setup Palo Alto in gns3 here, then you should be good to go.
We use the same management interface from the previous lab, so follow the previous guide and come back here again.
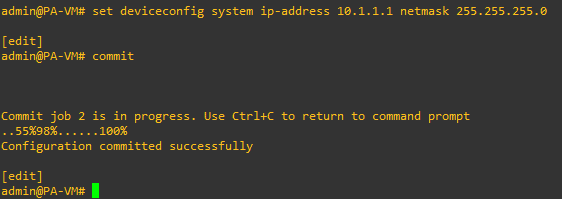
To configure the firewall management interface, log in to the firewall CLI console.
And enter the below commands.
configure set deviceconfig system type static set deviceconfig system ip-address 10.1.1.1 netmask 255.255.255.0 commit exit
2. Connect the switch to the Palo alto firewall.
Add a switch to the topology. Any switch would work as long as you can manage the VLAN via CLI.
I am using cisco VIOS from Cisco VIRL as the switch, and it should be connecting to the Firewall.
Drag and drop the switch to the topology, and connect both firewall management and the ethernet 1/2 interfaces to the switch on port G0/0 and G0/1, respectively.
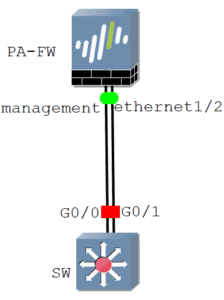
And turn on the switch.
Based on our topology, below is what we are going to configure on the switch.
| Interfaces | VLANS | Hosts |
| G0/0 | 10 | Palo Alto Management |
| G3/2 | 10 | Webterm (To access the Management GUI) |
| G3/3 | 10 | Local machine (To access the Management GUI) |
| G0/1 | 200 | Palo Alto ethernet 1/2 (Inside LAN network) |
| G0/2 | 200 | Inside-LAN-User1 |
| G1/1 | 200 | Inside-LAN-User1 |
| G1/0 | 200 | Webterm (To browse the Internet) |
Below is configuration from the switch.
configure terminal vlan 10 vlan 200 interface GigabitEthernet0/0 switchport mode access switchport access vlan 10 int GigabitEthernet3/2 switchport mode access switchport access vlan 10 int GigabitEthernet3/3 switchport mode access switchport access vlan 10 int GigabitEthernet0/1 switchport mode access switchport access vlan 200 int GigabitEthernet0/2 switchport mode access switchport access vlan 200 int GigabitEthernet1/1 switchport mode access switchport access vlan 200 int GigabitEthernet1/0 switchport mode access switchport access vlan 200 exit
Here is the VLAN output after the configuration.
Switch#sh vlan brief
VLAN Name Status Ports
---- -------------------------------- --------- -------------------------------
1 default active Gi0/3, Gi1/1, Gi1/2, Gi1/3
Gi2/0, Gi2/1, Gi2/2, Gi2/3
Gi3/0, Gi3/1
10 VLAN0010 active Gi0/0, Gi3/2, Gi3/3
200 VLAN0200 active Gi0/1, Gi0/2, Gi1/0
Make sure you validate the switch configuration in your lab before we proceed.
3. Connect management client to the switch.
We already covered how to add a Webterm client to the gns3. You may follow the same and connect the Webterm client to the port G3/2 on the switch.
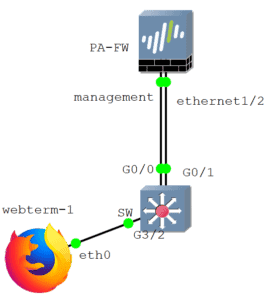
Let me try accessing the Palo alto management GUI from the webterm client.
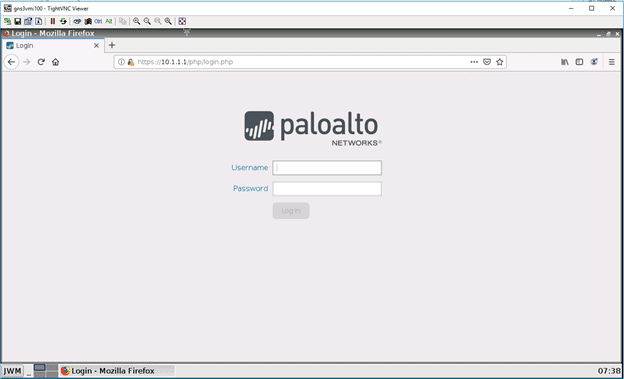
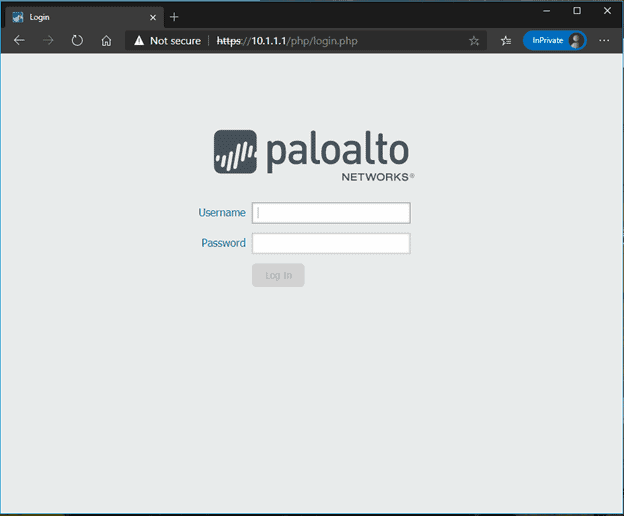
Open webterm and type the URL as https://10.1.1.10. You will be presented with the Firefox security screen, click on Accept the risk, and continue.
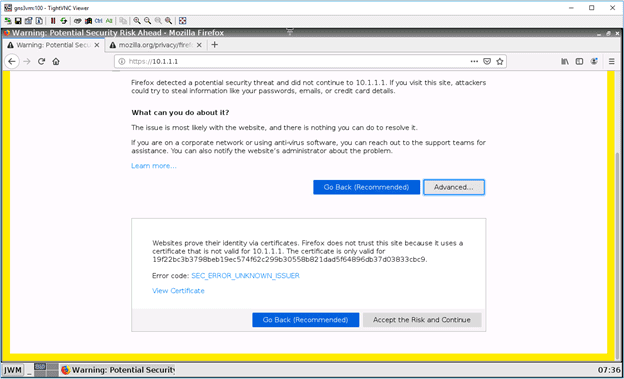
And you will now be presented with the login screen if you have configured the management IP and the switch correctly.
How to connect your local machine to access Palo Alto GUI?
I have already installed a VMware workstation pro on my client machine. You may download that and install it as well. You do not need to have a license. The trial license would work just fine, as we will not spin up any VM’s in it. It is for the configuration of the network interface.
Once you have the VMware workstation pro installed, you may open the VMware workstation and close it. It is for the VMware background process to start.
Then open gns3 and click on Edit – preferences, click on VMware, then Advanced local settings.
Change the VMnet adapter to 5, then click on Configure.
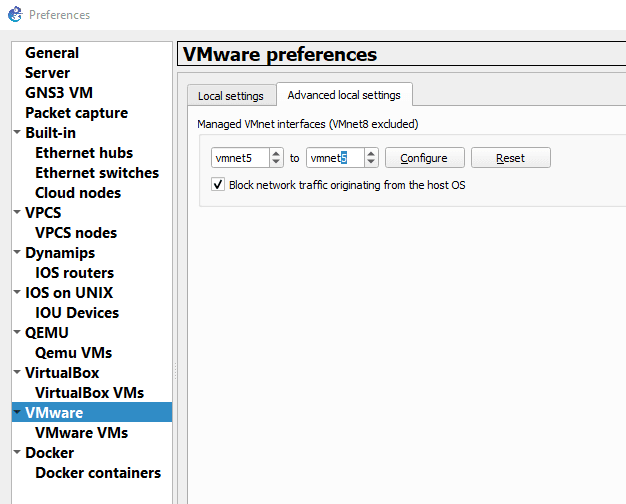
It should add the VMnet5 adapter to your local machine.
Configure the IP from the management subnet on your local machine.
Click start run, and type ncpa.cpl then click on OK.
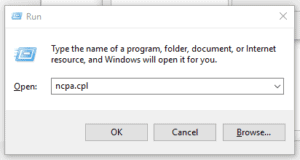
You should be able to see VMware network adapter VMnet5.
Right-click on the VMnet5 and properties, double click on the Internet Protocol Version 4.

Configure the Palo alto management subnet IP 10.1.1.15, then click on OK.

Add a cloud to the topology and right-click on the cloud icon and configure it.
Under Ethernet Interfaces, delete all other physical interfaces and check the box which says ‘Show special Ethernet interfaces.’
From the interface drop-down list, select VMware Network Adapter VMnet5, click on Add, and click on OK.
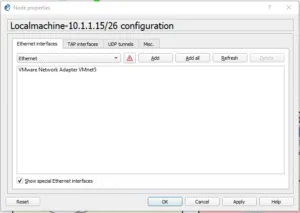
We just added the VMnet5 adapter to the topology.
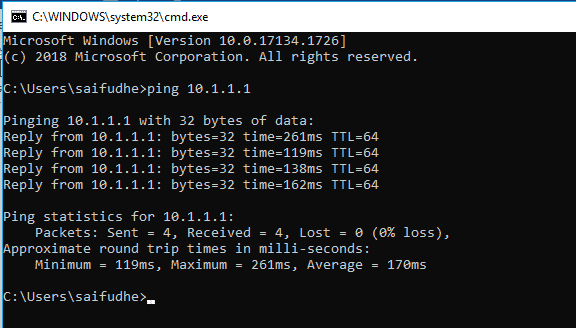
Connect the cloud to the switch port G3/3. At this point, you now should be able to ping the Palo alto management IP from your local machine.
Yes, as you can see, we can ping the IP now.
Let’s try accessing the Palo alto Management GUI from the local machine as well.
As you can see below, I tried to access the GUI from my local chrome browser, and I can access it.
I have covered the above steps in more detail here, you may check it out if you are confused with the steps above and more details around it.
4. Configure the Outside interface.
Similar to what we have configured in the last section, we can add the Internet cloud to the topology and connect to the firewall interface ehternet1/1.
Note: Make sure you use the Internet shared interface VMnet2 to connect to the cloud.
This link would act as an ISP.
When it prompts you to choose the server, select your local machine.
If you have any confusion about how you can do that, I highly recommend you go back and check the previous blog.

In a real scenario, the internet interfaces are kept under the untrusted outside zone.
You just connected the outside interface. Let us go ahead and configure the IP address to it.
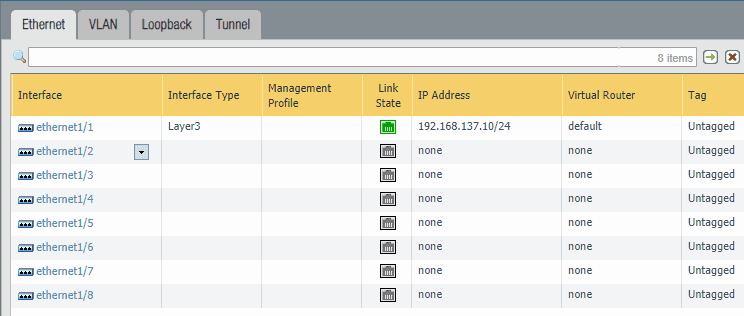
For the creation of a Layer3 interface with an IP address, let’s configure the interface ethernet1/1 with the IP address 192.168.137.10
In the last configuration lab, we used DHCP IP, but now we will configure the Firewall with a static IP.
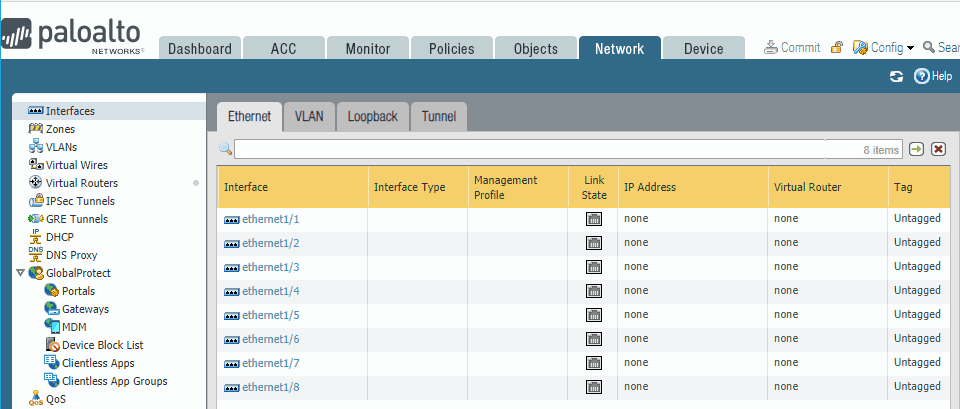
- Click on Network and then click on the interface on the left.
- To configure the interface ethernet1/1, just click on it.
- Change the interface type to Layer3. From the virtual Router, drop-down select the default one.
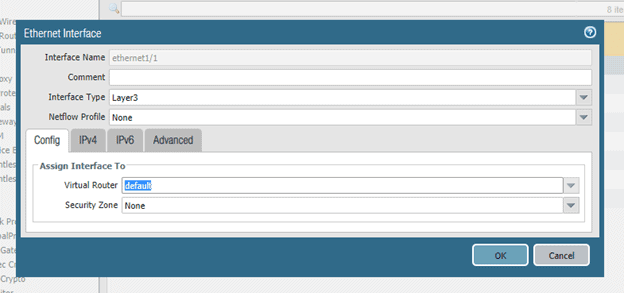
Now click on IPv4 tab and click on Add.
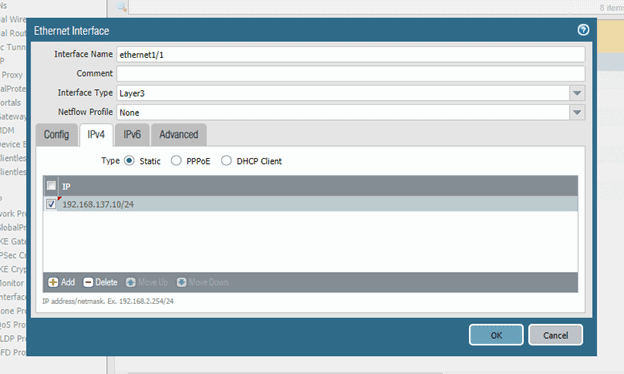
After adding the IP click on Ok.
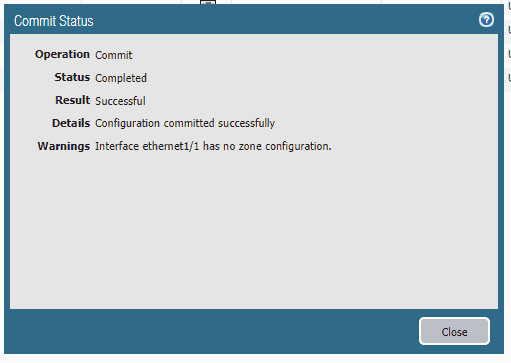
Commit the configuration by clicking commit on the top right corner.
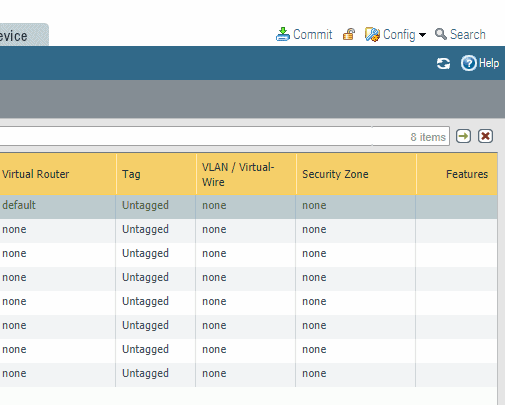
In the Palo alto commit window, click on Commit.
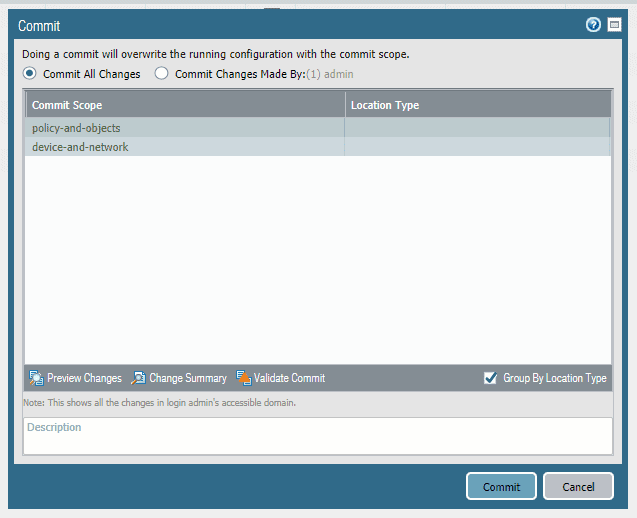
You should see the Commit was successful, but did you notice a Warning that says Interface ethernet1/1 has no zone configuration. We will create the zone next.
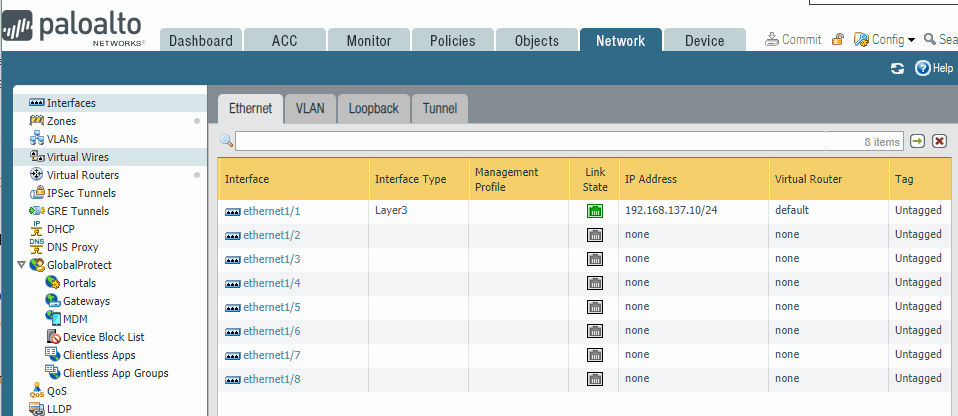
You should be able to see the outside interface that we just added, showing green now.
Which means the interface physical link status is good.
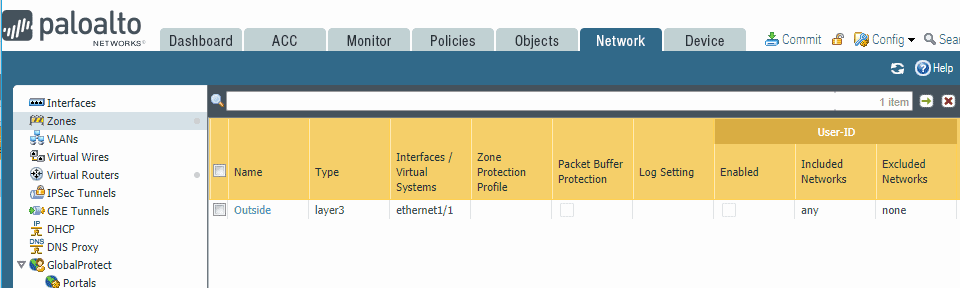
5. Create the outside zone.
As I stated before, I will go ahead and add the outside zone and put the ISP interface into it.
- To create a Zone, Click on Network and click on Zones on the left side.
- From the bottom, click on Add to add zones.
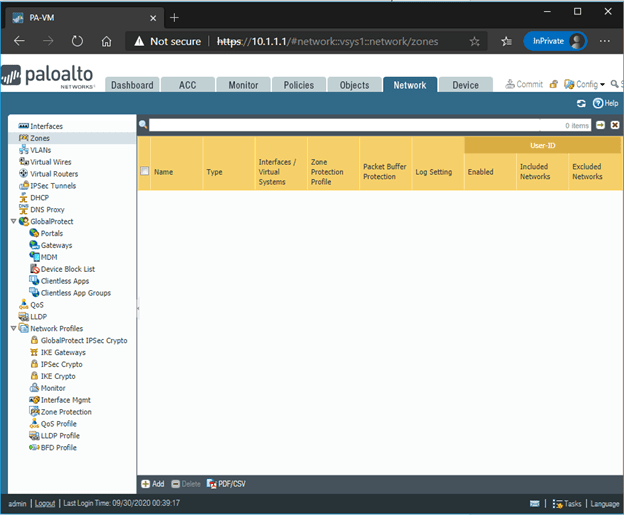
- Mention the zone name as Outside.
- And the interface Type Layer3
- In the list of interfaces, add ethernet1/1 and then click on OK.
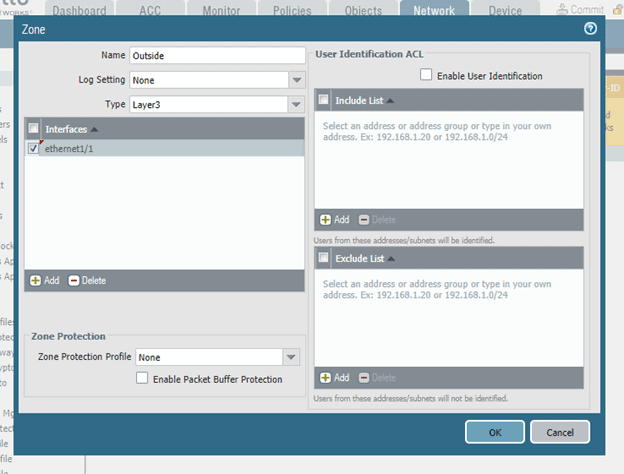
You can commit the changes now.
Verify the Uplink connectivity.
On the Firewall CLI, let’s try to ping the default gateway of the outside interface ethernet1/1, which is 192.168.137.1
admin@PA-VM> ping source 192.168.137.10 count 4 host 192.168.137.1 PING 192.168.137.1 (192.168.137.1) from 192.168.137.10 : 56(84) bytes of data. 64 bytes from 192.168.137.1: icmp_seq=1 ttl=128 time=115 ms 64 bytes from 192.168.137.1: icmp_seq=2 ttl=128 time=114 ms 64 bytes from 192.168.137.1: icmp_seq=3 ttl=128 time=109 ms 64 bytes from 192.168.137.1: icmp_seq=4 ttl=128 time=115 ms --- 192.168.137.1 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 3003ms rtt min/avg/max/mdev = 109.224/113.925/115.943/2.754 ms admin@PA-VM>
As you can see, I can ping, which means I can reach the ISP gateway.
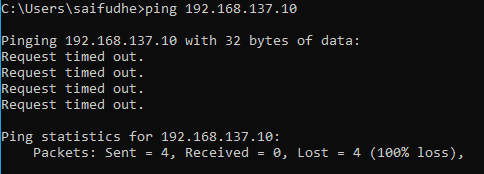
Let me also try pinging from the default gateway (my local machine configured with VMnet2 – 192.168.137.1) to the Firewall’s outside interface- 192.168.137.10.
We are not able to ping the Firewall outside IP from outside.
6. Configure the routing for the outside interface.
The outside interface is the edge of the Network. If anyone has to go out and be reachable on the Internet, you have to configure a default route.
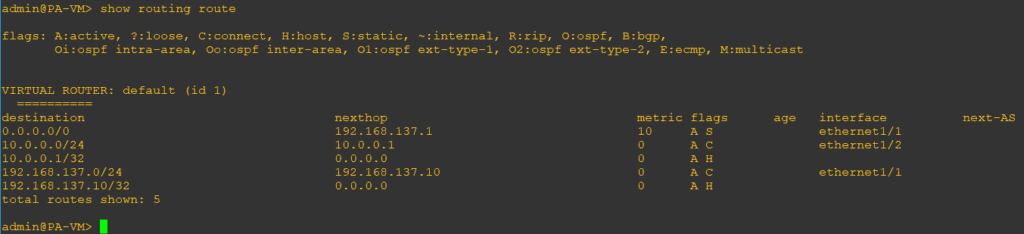
Let’s check the routing on the Palo alto firewall now.
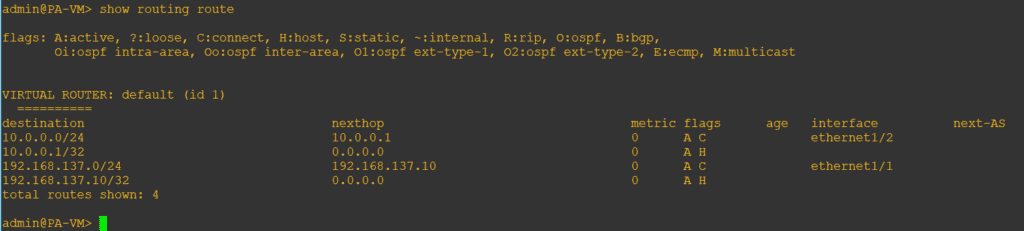
As you can see, I don’t have the default route towards the Internet. Let’s go ahead and add that now.
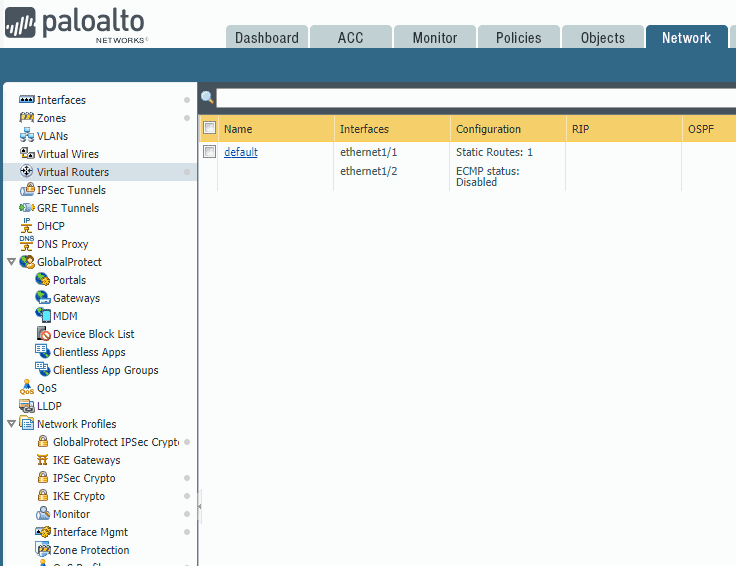
To add the Palo Alto firewall route, you can click on Network and then click on Virtual routers.
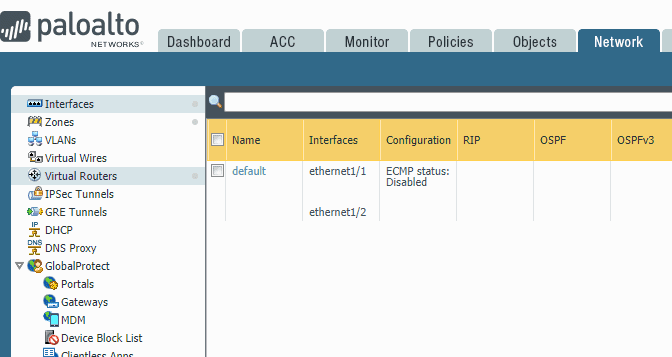
And then click on the Router.
On the virtual Router prompt, click on Static routes.
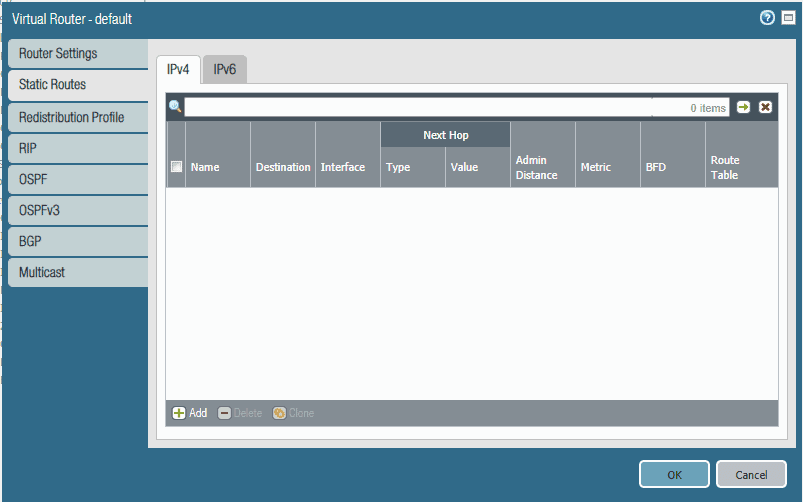
Click on Add to add the routes.
Name: Route to Internet
Destination : 0.0.0.0/0
Interface : ethernet1/1 #outside interface
Next hope: 192.168.137.1. This should be the ISP gateway.
Leave everything else to default, then click on OK. And commit the changes.
When you check the routing with the command show routing route now, you should see the default route pointing it to the Internet Gateway.
7. How do I Allow Ping to the Firewall outside interface?
In the real-world, some users would allow Ping to outside IP, and some of them don’t. However, we are going to allow Ping on this configuration.
Click on the Network tab and then click on Interface Mgmt.
Click on Add to create a new interface profile with the name Ping-allow and check the Ping options under Network services.
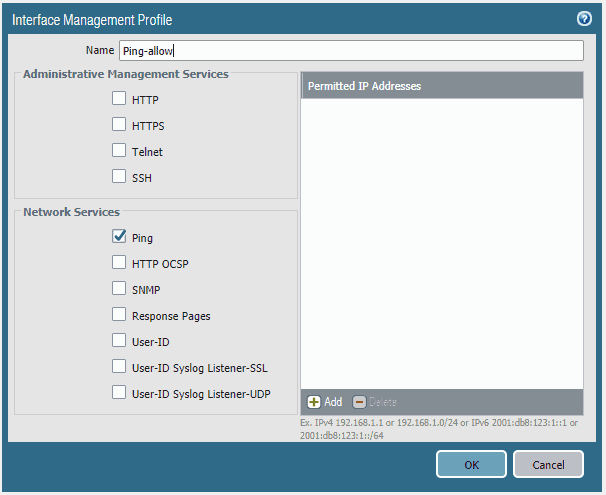
You can allow permitted IP addresses that can ping as well.
For example, you can configure only your registered public IP’s and RFC1918 private ranges to Ping the Firewall’s external IP in a production environment.
Note: Be careful that you are not checking the ssh or https option to the public. By doing so, you expose your administrating management via the public Internet, which is not good.
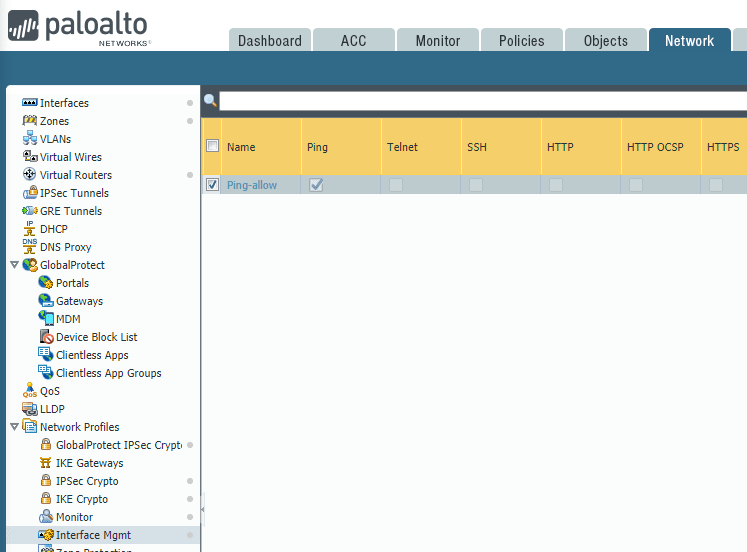
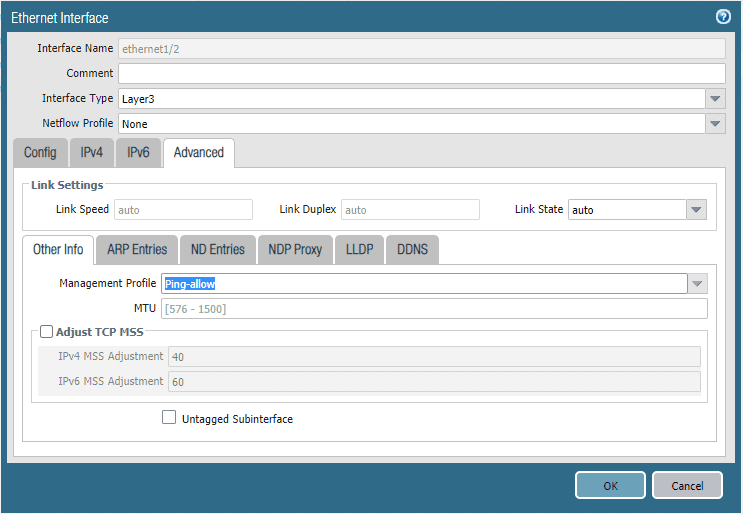
I configured the interface Management profile, as you can see below.
You may now go back to the interface under Network and click on ethernet1/1 click on Advanced.
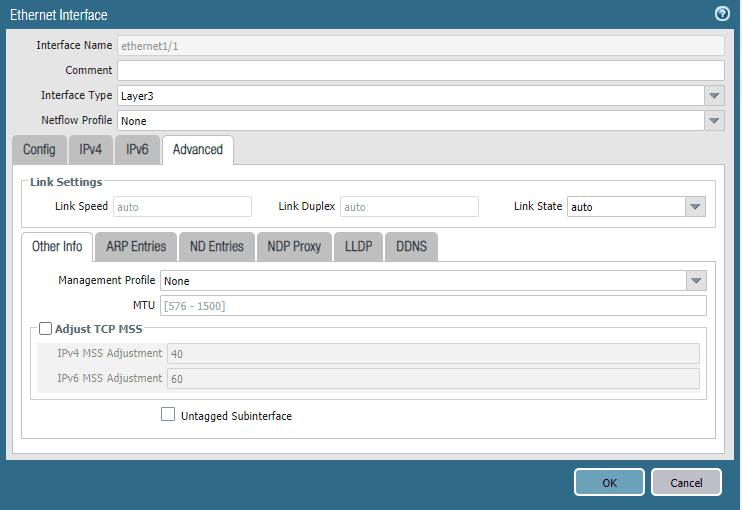
Under the management profile, select the Ping-allow profile that you have created and then click on OK.
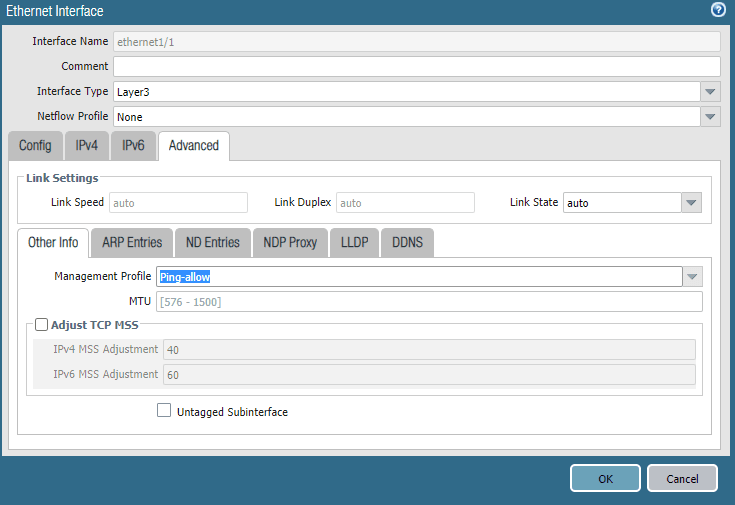
You may now commit the change.
Verification.
We just configured to allow Ping on the outside interface. Let us test it out by pinging the outside interface from your local machine.
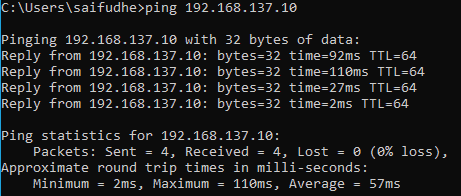
As you can see, I can ping the Firewall outside interface from my local machine.
8. How to Configure the internal interface?
Similar to the outside interface, let’s Configure the internal interface, which should act as a Gateway for the LAN users.
We will be configuring ethernet1/2 for this.
- Click on Network and then click on the interface on the left. You can see only the outside interface configured at the moment.
Click on the interface ethernet1/2
Change it to Layer3, and select the default as the virtual router
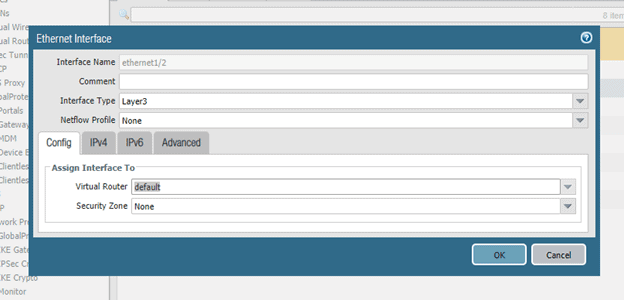
- Once the config part is done, click on IPv4.
- Add the IP address as per the diagram, 10.0.0.1/24 and Click on OK.
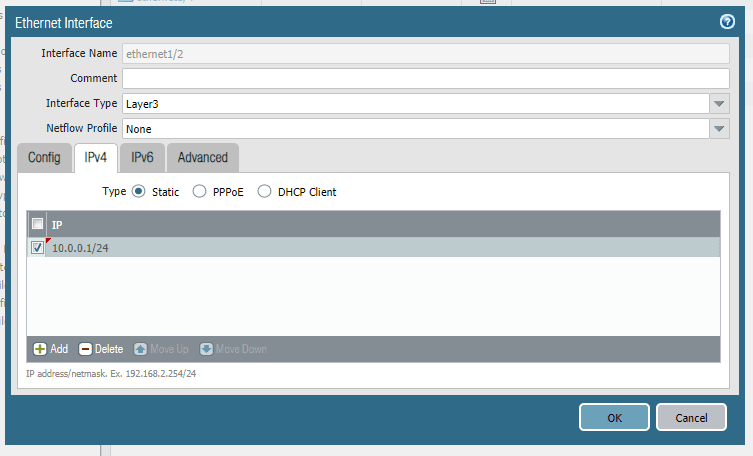
Commit the changes now to take the configuration to take place.
While committing, you should get a warning which says the interface ethernet1/2 is not part of the zone.
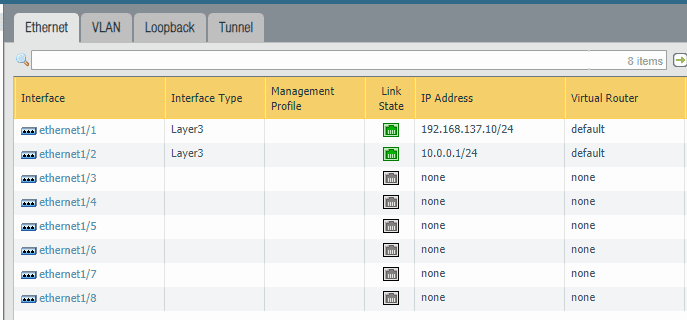
You should now have ethernet 1/2 configured with IP 10.0.0.1/24, but you cannot reach this IP yet.
9. Create the Inside zone for the Firewall.
Now let’s go ahead and create the second zone inside the Firewall.
The inside zone we can treat as a trusted zone as it would be the place where the employees are usually connected. Not a bad guy.
Click on Network and click on the zone on the left side.
On the bottom of the screen, click on Add. The zone creation window now pop up.
- On the name, type Inside.
- Interface type Layer3.
- add the inside interface, which is, in our case ethernet1/2
To add the interface etherenet1/2, click on Add under interfaces. Then click on OK.
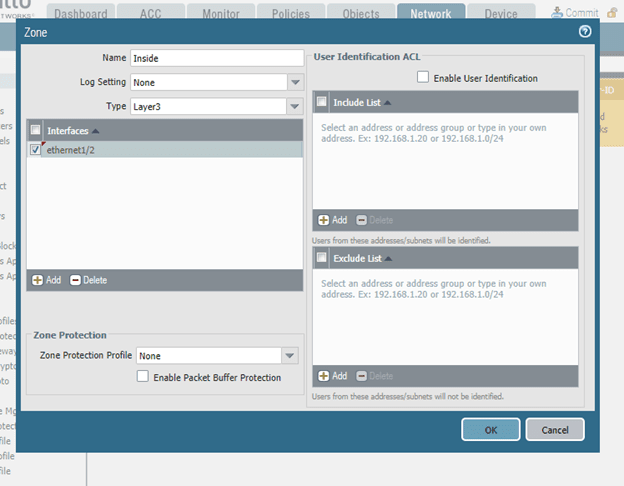
Let’s go ahead and commit the change that we have just made.
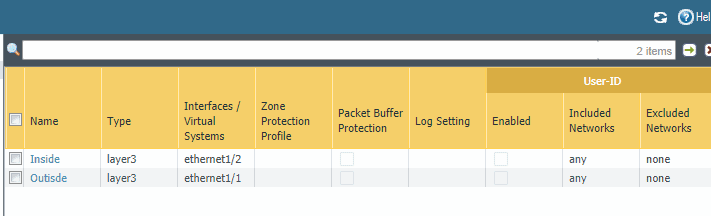
Under zone, now you should be able to see two zones with its respective interfaces.
10. Add LAN users to the Network.
To simulate the LAN network, I am going to use
- Add two cisco routers as an end-hosts.
- I am using the cisco VIRL ios image for this purpose. Any other cisco image would work. Even you don’t have a cisco image, that’s fine. You can still play with a webterm client.
- And One Webterm client again to browse internet connectivity.
- My local machine has multiple connections to this lab, and its not a good idea to keep the local machine again, attaching to the internal Network. As the test that we are going to perform will not work well.
Connect all the end-user hosts to the VLAN 200.
Add two cisco routers to the topology, and rename them as Inside-LAN-User1 and Inside-LAN-User2 and connect them to switch on port G0/2 and G1/0, respectively
You may change the symbol if you want to.
Below is the configuration from the Router.
Note: To make the Router act as an end-user host, I first disabled IP routing and configured the IP and default gateway.
Router(config)#host Router(config)#hostname Inside-LAN-User1 Inside-LAN-User1(config)#no ip routing Inside-LAN-User1(config)#ip default-gateway 10.0.0.1 Inside-LAN-User1(config)#int g0/0 Inside-LAN-User1(config-if)#ip add 10.0.0.10 255.255.255.0 Inside-LAN-User1(config-if)#no shut Inside-LAN-User1(config-if)#exit Inside-LAN-User1(config)# *Sep 30 08:08:15.313: %LINK-3-UPDOWN: Interface GigabitEthernet0/0, changed state to up *Sep 30 08:08:16.313: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0, changed state to up Inside-LAN-User1# *Sep 30 08:08:30.723: %SYS-5-CONFIG_I: Configured from console by console Inside-LAN-User1#wr Building configuration... [OK]
Similarly, configure the second cisco router host as well, just the IP would be different on the second host, instead of 10.0.0.10, we can use 10.0.0.20.
To simulate the end-user internet browsing, add a webterm client to the port G1/1
Let’s try to ping the default gateway that is configured on the Firewall inside interface ethernet1/2
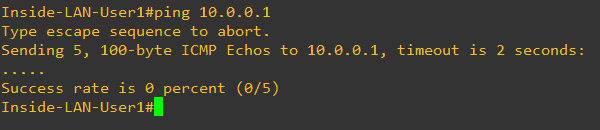
As you can see, we are not able to ping, do you know why?
If you answered, that’s because we haven’t enabled the ICMP ping on the internal interface, then you are right. Let’s go ahead and do that.
11. How to Allow PING on the internal interface?
We already configured the network management profile to allow Ping earlier for the outside interface.
Let’s go ahead and apply the same configuration on the internal interface ethernet1/2.
Click on Network and then click on interfaces.
Click on the interface ethernet1/2 and then click on Advanced.
In the management profile, select Ping-allow and click on OK.
Before we commit, let me send a continuous ping towards the gateway from an internal host and monitor the Network.
As you can see below, the Network was not reachable initially, and then it started to respond to my Ping, which means it worked.
Inside-LAN-User1#ping 10.0.0.1 rep 1000 Type escape sequence to abort. Sending 1000, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds: ......!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! !!!!!!!!!!!!!!!!!!!! Success rate is 96 percent (226/235), round-trip min/avg/max = 1/1/6 ms Inside-LAN-User1#
We will also try to ping from the second end-user machine to make sure we can reach the gateway from there.
Inside-LAN-User2#ping 10.0.0.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/2 ms Inside-LAN-User2#
How do I connect my Palo Alto firewall to the Internet?
The LAN network is working fine, and the Management network is also looking good. Let’s go ahead and configure the WAN side.
From the Firewall, you should reach the Internet as we have configured the default route on the Firewall’s edge.
admin@PA-VM> ping count 4 source 192.168.137.10 host 8.8.8.8 PING 8.8.8.8 (8.8.8.8) from 192.168.137.10 : 56(84) bytes of data. 64 bytes from 8.8.8.8: icmp_seq=1 ttl=117 time=19.9 ms 64 bytes from 8.8.8.8: icmp_seq=2 ttl=117 time=18.6 ms 64 bytes from 8.8.8.8: icmp_seq=3 ttl=117 time=19.3 ms 64 bytes from 8.8.8.8: icmp_seq=4 ttl=117 time=26.8 ms --- 8.8.8.8 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 3003ms rtt min/avg/max/mdev = 18.647/21.186/26.882/3.319 ms admin@PA-VM>
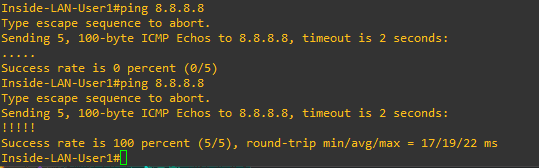
Yes, I can reach the Internet on the Firewall, which is good. How about from the end-user machine. Should I be able to communicate?
As you can see, I am not able to ping the public IP, which is 8.8.8.8
Inside-LAN-User1#ping 8.8.8.8 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 8.8.8.8, timeout is 2 seconds: ..... Success rate is 0 percent (0/5) Inside-LAN-User1#
So which means I got access to the Internet from ISP, and the WAN side is good. How do I let my end-user machine to talk to the Internet now?
12. Configure security policies to allow inside to outside.
So you have to do two things here.
First, you need to allow the end-user to talk to the Internet, allowing inside zone IP segment 10.0.0.0/24 to talk to the outside zone using firewall security policies.
Second You will have to also configure the NAT for the IP subnet 10.0.0.0/24
From an internal host, let’s see if you can reach the outside interface of the Firewall.
Inside-LAN-User1# Inside-LAN-User1#ping 192.168.137.10 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.137.10, timeout is 2 seconds: ..... Success rate is 0 percent (0/5) Inside-LAN-User1#
As you can see, we are not able to ping the outside interface of the Firewall. Let’s go ahead and fix that.
In the Paloalto firewall GUI, click on Policies and click on security on the left side.
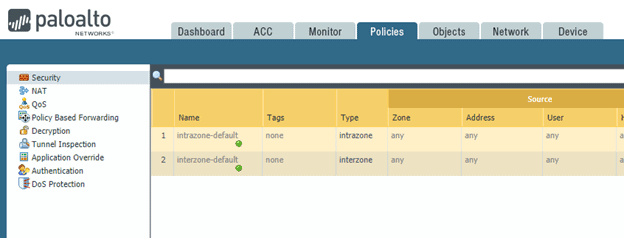
By default, you should be able to see two policies, Interzone-default and Interzone-default.
Let’s create a policy by clicking the add button down below.
In the Security Policy rule, Enter the name Allow-inside-LAN-to-Outside. You can add a description if you want.
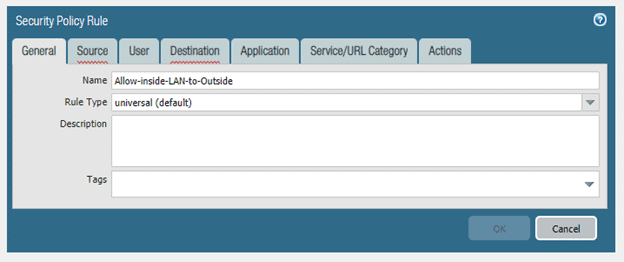
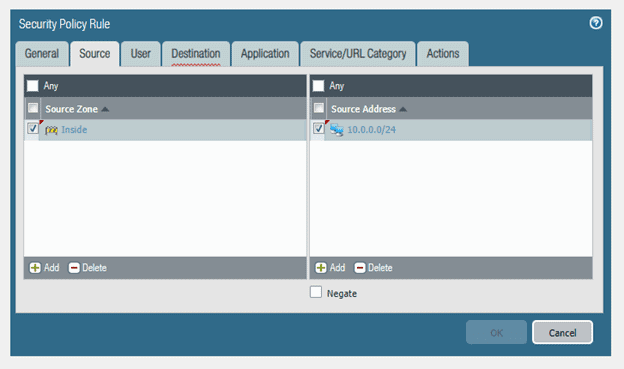
Click on the source tab.
When the end-user machine in our LAN is going out to the Internet, it means that the LAN source is inside and the destination is outside
From the Source zone, select Inside zone by clicking add. You can also specify the source zone address, which is, in our case, 10.0.0.0/24
Click on the Destination tab now.
Here you need to specify the destination zone, which is outside.
Since we are going to allow internet access, the destination IP could be anything. So you may check Any
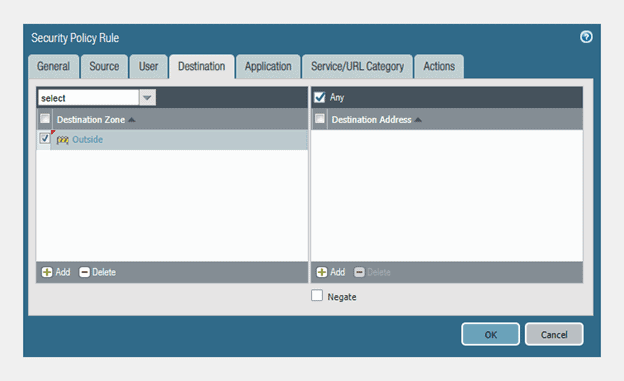
If you wanted to specify a specific website, you could add its IP address here. That way, the end-user only can talk to that IP.
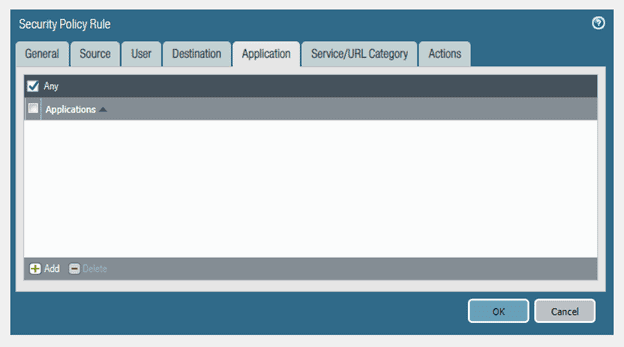
You can also specify the Application if you want. I am just leaving it as any.
Neither I am going to make any changes to the Service/URL category.
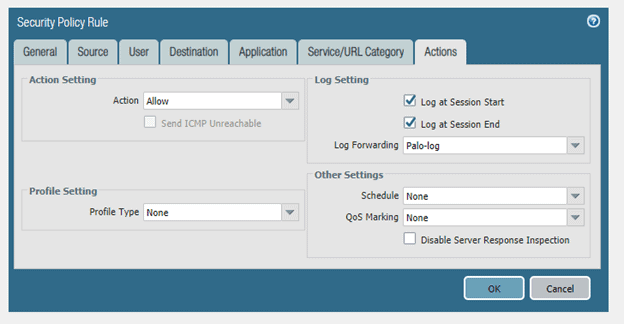
Click on Action. You need to make sure that the Action is to allow the connection. You may check on Log at Session start as well.
I also created a log called Palo-Log. Click on OK here.
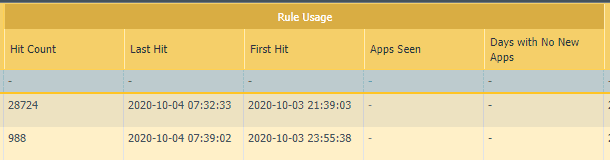
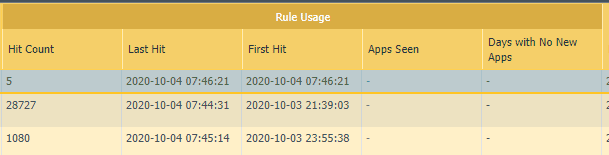
Before we commit, just check the HIT count on the policy we just made on the right side under Rule Usage.
Commit the policy change that you just made.
Let me verify if I can reach the outside interface from the inside now.
Inside-LAN-User1#ping 192.168.137.10 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.137.10, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/5/7 ms Inside-LAN-User1#
Awesome! that worked. Let me check the hit count now.
As you can see, there are about five hits on the policy that we just made.
Alright, we just allowed the Network. Does that mean you can now talk to the Internet from the LAN side?
No! we just allowed the inside Network to talk to the outside. Since the internal Network uses private IP, you need to translate to public IP to reach the Internet.
Note: Though we are using Private IP 192.168.137.0/24 as the internet IP, let’s assume for this lab that it is a public range
13. Configure NAT on the Palo alto firewall.
To configure the NAT policies in the Palo Alto firewall, you can click on the Policies and click on NAT.
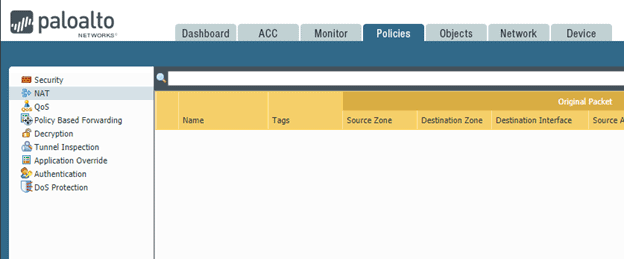
I don’t have any NAT configured currently.
Let me do that now by clicking Add.
Just give the NAT policy rule a name, I am giving LAN-TO-OUT
I would highly recommend that you start adding a description to your policies from now on. Not doing so will be difficult in the long run when you wanted to look at some of the polices.
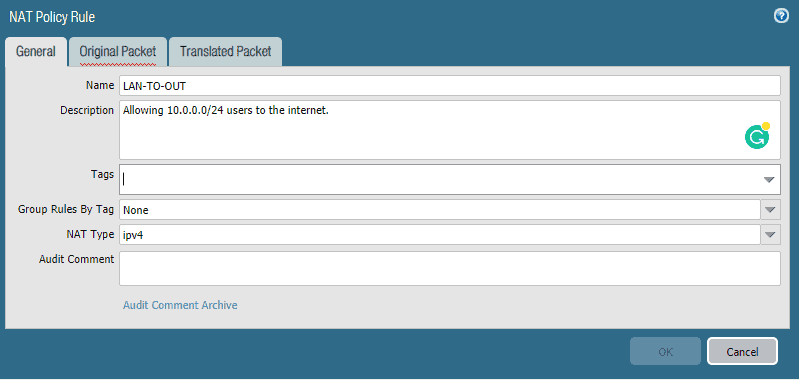
Click on Original Packet.
In the Source zone, pick the inside zone, Destination zone select outside, and the source Address add the LAN subnet 10.0.0.0/24, then click on OK.
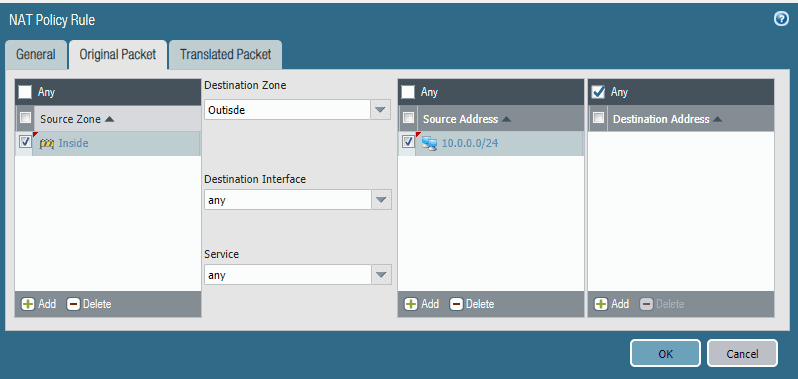
You may now click on the Translated packet tab.
When you click on the Translation Type, you should be able to see different types of NATs.
We will use Dynamic IP and Port. it would translate multiple users in the private Network to single or multiple public IP’s using different port numbers.
It will translate multiple hosts in the private networks to single or more public IP using different port numbers.
In the translation type, I am selecting the Dynamic IP And port.
Address Type Interface address
Interface: ethernet1/1
On the Destination Address translation, you may select none in the Translation Type.
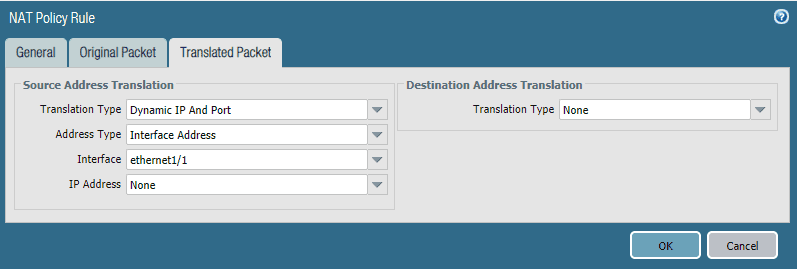
That’s it. You may commit the changes now, and if everything went well, you should be able to talk to the Internet IP’s from the inside machines.
I just got the message which says Commit was successful. Let’s go ahead and try to ping the google public DNS IP from my local machine.
If you try to ping www.google.com, you will not be able to ping because you haven’t enabled the IP domain-lookup. We have not configured the DNS server on the cisco router either, which I am using as an end userbox. Let’s do that as well.
Inside-LAN-User1#ping www.google.com Translating "www.google.com" % Unrecognized host or address, or protocol not running.
Let’s make some changes.
Inside-LAN-User1#conf t Enter configuration commands, one per line. End with CNTL/Z. Inside-LAN-User1(config)#ip domain-lookup Inside-LAN-User1(config)#ip name-server 8.8.8.8 Inside-LAN-User1(config)#exit Inside-LAN-User1#wr Building configuration... [OK] Inside-LAN-User1# *Sep 30 13:18:50.249: %GRUB-5-CONFIG_WRITING: GRUB configuration is being updated on disk. Please wait... *Sep 30 13:18:50.861: %GRUB-5-CONFIG_WRITTEN: GRUB configuration was written to disk successfully. Inside-LAN-User1#
When I try to ping the google now, we can reach google.com from my internal machine.
Inside-LAN-User1#ping www.google.com *Sep 30 13:15:47.894: %SYS-5-CONFIG_I: Configured from console by console Inside-LAN-User1#ping www.google.com Translating "www.google.com"...domain server (8.8.8.8) [OK] Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 142.250.71.36, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 17/18/20 ms Inside-LAN-User1#
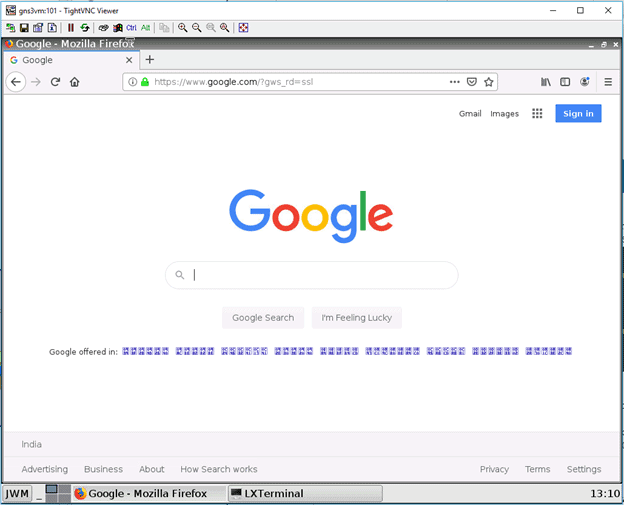
Let me try to browse the Internet now from the webterm client.
Configure the Webterm with the below IP configurations.
# Static config for eth0 auto eth0 iface eth0 inet static address 10.0.0.25 netmask 255.255.255.0 gateway 10.0.0.1 up echo nameserver 8.8.8.8 > /etc/resolv.conf # DHCP config for eth0 # auto eth0 # iface eth0 inet dhcp
After you applied the configuration and try to access the Internet, you can access it from Webterm now.
Alright, we configured the Palo alto firewall on the Network successfully, when I started to write this post, I never thought it would be this long. But eventually, it becomes the longest post in my blog.
Try this lab yourself from step one, as I have configured this as a step-by-step guide, and you should be able to complete it if you follow this along easily. Let me know how it went for you in the comments 😊