If you are new to networking you must have heard the term called ARP protocol – address resolution protocol many times.
You may be wondering or even confused. Well, what is the ARP protocol and how ARP works in the real world?
Before we talk about how arp works we need to know something called a mac address first.
What does MAC address mean?
MAC ( Media Access Control ) address is a 48-bits long burned in address on all the NIC (Network interface card) out there.
Every network device will have NIC and its Mac addresses. Be it a laptop, smartphone, iPad, routers and switches, etc. and it’s unique on all the devices.
MAC addresses are also known as hardware addresses or physical addresses and it also called Layer 2 addresses, meaning it works in the Data link layer of the OSI model.
You may already know that all the computers can communicate over the network via IP addresses but if you think about it, it’s not just an IP address, it also requires a MAC address.
What is ARP used for in networking?
We identified that on an Ethernet network, devices need MAC addresses to communicate with each other, not just IP addresses.
ARP protocol is a network protocol that dynamically maps an IP address to a MAC address or physical address on the ethernet network segment.
Devices looking for MAC address sends an arp request, and the device with the right MAC address would respond to that with an arp reply.
And the hosts on the network would keep a record of its IP addresses and MAC addresses in its ARP table/ARP cache on the operating system so that it doesn’t need to go through the same arp process again
How do I see the ARP table?
All the mac and IP mapping you can see them in the Arp table, each operating system uses it’s own commands to see the arp table.
First, let’s look at the Windows machine.
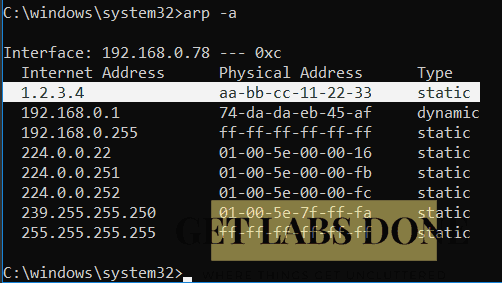
In windows, you can type arp -a to get the ARP table.
C:\Users\saifudhe>arp -a Interface: 192.168.0.78 --- 0xc Internet Address Physical Address Type 192.168.0.1 74-da-da-eb-45-af dynamic 192.168.0.255 ff-ff-ff-ff-ff-ff static 224.0.0.22 01-00-5e-00-00-16 static 224.0.0.251 01-00-5e-00-00-fb static 224.0.0.252 01-00-5e-00-00-fc static 239.255.255.250 01-00-5e-7f-ff-fa static 255.255.255.255 ff-ff-ff-ff-ff-ff static C:\Users\saifudhe>
As you can see above, you have 192.168.0.1 which is my Dlink router’s IP address and you could see its physical address ( MAC address ) associated with it and its learned via dynamic.
Along with other IP addresses, you can also see a static entry. But those static ARP entries are not added by me its added by the windows Operating system.
How do I create a static ARP entry in Windows 10?
The ARP entry can be static or dynamic, If you wanted to create a static ARP entry in windows you can do so by entering the below command, you will have to map the MAC address to the IP address manually.
arp -s 1.2.3.4 aa-bb-cc-11-22-33
Now when I look into the ARP table again I can see that the new ARP entry is added.
Remove static arp entry windows
How do I delete the arp entry which we just added? you can simply type below command.
arp -d 1.2.3.4
In linux you can type arp -a
Both windows and Linux manage the ARP table similar way, except a few differences, so let’s look at how to manage the ARP table in Linux.
[root@getlabsdone ~]# arp -a gateway (192.168.1.1) at 94:3f:c2:a0:84:65 [ether] on ens1 [root@getlabsdone ~]#
We can only see the default gateway dynamic arp entry in this Linux box.
How to Add static ARP entry Linux?
Similar to how we added the static arp entry in windows, you can do the same thing in Linux as well. If you wanted to add an entry you may do so by typing arp -s
‘S’ stands for static here.
[Solution] SIOCSARP: Network is unreachable
I tried to add static arp entry just like how I did it for windows, but I got an error in Redhat Linux.
[root@getlabsdone]# arp -s 1.2.3.4 aa:bb:cc:11:22:33 SIOCSARP: Network is unreachable
I tried with different subnet but same error
[root@getlabsdone]# arp -s 10.1.1.1 aa:bb:cc:11:22:33 SIOCSARP: Network is unreachable
Why are we getting an error when adding the static arp in Linux?
Unlike Windows, In Linux, you can only add local subnets to the arp entries. Since we tried to use a different subnet we got the error “SIOCSARP: Network is unreachable”
The reason we are not able to add different subnets because any other subnets will send to the default gateway by default.
Let’s try to add static MAC for your local subnet, and see what happens, see below. we added four static ARP entries and it was successful.
[root@getlabsdone]# arp -s 192.168.1.2 aa:bb:cc:11:22:33 [root@getlabsdone]# arp -s 192.168.1.3 aa:bb:cc:11:22:33 [root@getlabsdone]# arp -s 192.168.1.4 aa:bb:cc:11:22:34 [root@getlabsdone]# arp -s 192.168.1.5 aa:bb:cc:11:22:35
To verify this configuration you can do arp -a which will show you all the static arp entries that you have just added.
[root@getlabsdone]# arp -a ? (192.168.1.4) at aa:bb:cc:11:22:34 [ether] PERM on ens1 ? (192.168.1.3) at aa:bb:cc:11:22:33 [ether] PERM on ens1 gateway (192.168.1.1) at 94:3f:c2:a0:84:65 [ether] on ens1 ? (192.168.1.5) at aa:bb:cc:11:22:35 [ether] PERM on ens1 ? (192.168.1.2) at aa:bb:cc:11:22:33 [ether] PERM on ens1
You can also change your default gateways Mac address.
arp -s 192.168.1.1 aa:bb:cc:11:22:33
Note: if you are making changes to the default gateway MAC address you got to be a little careful while you are connected to the device remotely. Altering the default gateway mac address while you are in the same network will break the network connectivity.
How to clear ARP cache in Linux?
Use can use the command below to delete the arp entry which I just added
arp -d 192.168.1.1 arp -d 192.168.1.2 arp -d 192.168.1.3 arp -d 192.168.1.4 arp -d 192.168.1.5
here ‘d’ stands for delete
In my opinion, the best way to understand the arp process is by visualizing them.
Rather than just staring at the CLI screen and scratching your head thinking. Okay, they say it works this way and that must be it, without giving much of a thought.
What is ARP process?
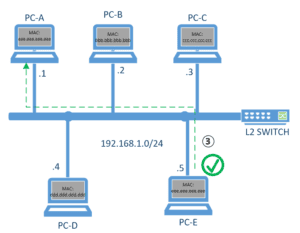
let’s suppose we have two computers, PC-A and PC-E with IP address of 192.168.1.1 and 192.168.1.5 respectively.
When you try to ping PC-E from PC-A, it doesn’t send the ICMP (ping packet) packet right away, does it?
It doesn’t, because PC-A doesn’t have any clue about PC-E’s MAC address and its path. But how does PC-E can communicate with PC-E then, the answer to this question is ARP protocol – address resolution protocol.
Lets look into the ARP process steps.
In this example below.
PC-A trying ping PC-E.
Step 1. ARP request Broadcast.
This ARP request broadcast frame sends to all the interfaces on the switch where all the PCs are connected except the PA-A interface.
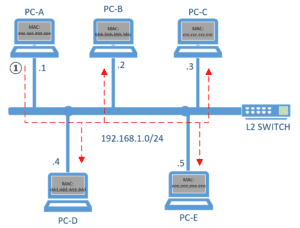
Step 2. Discard the ARP request.
All network hosts connected to the switch will drop the broadcast as that ARP broadcast doesn’t belong to them except PC-E
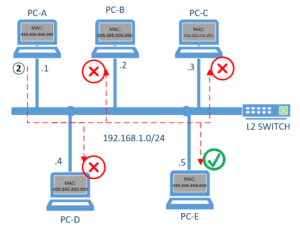
Step3. ARP Reply Unicast.
PC-E acknowledges the broadcast and reply saying that
Hey! 192.168.1.5 belongs to me and here is my mac address which is “eee.eee.eee.eee” and this time ARP reply would be unicast not broadcast as PC-E already knew about the PC-A’s mac address (source MAC) during the initial ARP request
What is ARP protocol in Wireshark?
let’s simplify this whole Arp process using Wireshark, by the end of this article you will have a pretty good idea of what is arp protocol.
Here I am using two Routers to simulate computers, I will show you how.
Note: I am using a GNS3 to virtualize the environment.
In gns3 add two routers and one switch and connect both as below. I also changed the router symbol to a computer by right-clicking on the gns3.
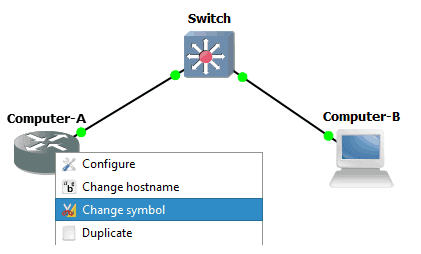
We can console into the PC by double-clicking on the computer icon and make changes on both routers as below to make the router act as a computer. also, configure the IP address on both sides.
Computer A
Router#conf terminal Router(config)#hostname Computer-A Computer-A(config)#no ip routing #it disables the routing capabilities of the router Computer-A(config)#int gigabitEthernet 0/0 Computer-A(config-if)#ip add 192.168.1.1 255.255.255.0 Computer-A(config)#exit Computer-A#
Computer B
Router#conf terminal Router(config)#hostname Computer-B Computer-B(config)#no ip routing Computer-B(config)#int gigabitEthernet 0/0 Computer-A(config-if)#ip add 192.168.1.2 255.255.255.0 Computer-B(config)#exit Computer-B#
Capture the Wireshark Capture.
Let’s start the packet capture by clicking on Start Capture, this will start the Wireshark packet capture on this network in the background. Also, click on the start of the capture visualization program.
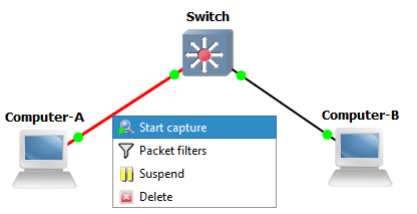
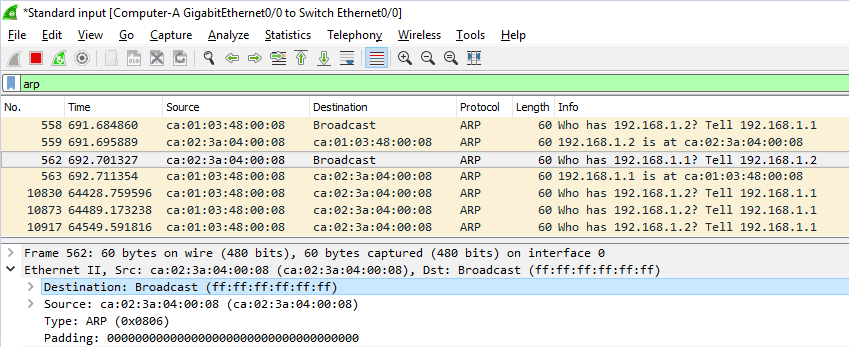
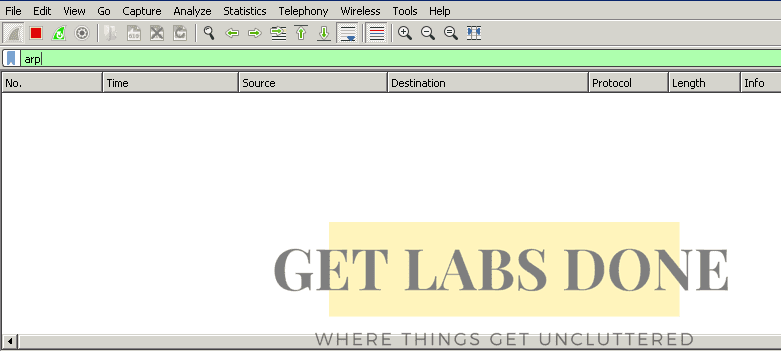
Wireshark just got opened and we do see multiple traffic, but our focus is mainly to see and analyze the ARP traffic.
How to filter ARP traffic in Wireshark?
To see specifically arp protocol traffic in Wireshark, you can put the filter by typing ‘arp’ in lower case in the Wireshark filter box to see the ARP traffic. We don’t see anything at the moment for the Arp process in Wireshark. Let’s generate some traffic using PING (ICMP)
Generate ARP request using ICMP.
The best way to simulate the ARP process in the network is by generating some traffic, let’s send some ICMP packet.
Before you do that make sure to check the arp table to see if it’s empty for the address 192.168.1.2 or not.
I don’t see any arp entry at the moment. I can only see the arp entry for its local interface which is expected behavior.
Computer A#show ip arp Protocol Address Age (min) Hardware Addr Type Interface Internet 192.168.1.1 - ca01.7d7e.0000 ARPA GigabitEthernet0/0
Computer-A#show ip interface brief Interface IP-Address OK? Method Status Protocol GigabitEthernet0/0 192.168.1.1 YES manual up up
if there is something you may have to clear the arp cache and start this step again. You can clear the arp entry in cisco router by typing, clear ip arp and the IP address
Let’s do a ping from computer B to Computer A
Computer-A#ping 192.168.1.2 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.1.2, timeout is 2 seconds: .!!!! Success rate is 80 percent (4/5), round-trip min/avg/max = 16/19/24 ms Computer-A#
Why does first ping fails?
Did you notice that our first ping failed? It’s because Computer A is not aware of the IP address 192.168.1.2 yet. Hence it started the ARP process to identify where the MAC address is. So the First ping failed due to the ARP process.
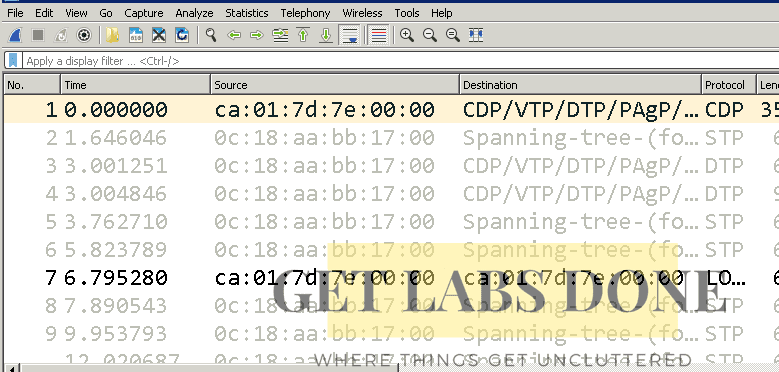
We can also see that, the moment we initiated the ping, the ARP process started in Wireshark as well.

let’s break it down and see what just happened here.
Let me change the time column to hostname to make more sense.

I differentiated these machines with its mac address only to understand this process better for this lab, , Mac address ca01.7d7e.0000 belongs to Compute-A and the mac address ca02.7d8c.0000 belongs to Computer-B. But eventually, we are trying to get the mac address of computer B, which won't be the case for the real network. In the real network, we will not know about the Computer-B mac address.
ARP packet format Wireshark
We got the packet capture ready, and its time for us to analyse the packet and understand the ARP using the wireshark capture.
Step1. ARP Broadcast request
1. On the first Frame, you can notice an arp broadcast is sent to the special mac address ff:ff:ff:ff:ff:ff which is broadcast MAC address, because the ComputerA doesn’t know the mac address of the Computer B and it looking for the assigned MAC address of Computer B.

2.As you can see Target MAC address which is nothing but the destination mac address shown as 00:00:00:00:00: 00, which means this frame doesn’t have the destination MAC hence put this value. As we already know the destination IP you could see the Target IP address as 192.168.1.2.
3. In the Frame you can also see the Type as ARP, in the end, it has written in Hexadecimal format 0x0806 indicates its an ARP type.
4. On the top right corner, you will be able to see info in Wireshark which basically translates in a human-readable format, who has 192.168.1.2? Tell 192.168.1.1
Step2. ARP reply
On the second Frame, only Computer-B in the ethernet segment sends ARP reply to the arp broadcast message saying that, hey the IP address 192.168.1.2 belong to the mac address ca02.7d8c.0000

Is ARP reply unicast or Broadcast?
You can see from the Wireshark packet capture output that, we already have the source and destination mac addresses, which means Arp reply is unicast, not Broadcast.
Down below you could see MAC and IP association.
Let’s look at Computer-A arp table and see what it has got. You can see that by typing show IP arp in Computer-A, it shows the Computer-B IP address 192.168.1.2 and its associated mac address has been learned by Computer-A
Computer-A #show ip arp Protocol Address Age (min) Hardware Addr Type Interface Internet 192.168.1.1 - ca01.7d7e.0000 ARPA GigabitEthernet0/0 Internet 192.168.1.2 48 ca02.7d8c.0000 ARPA GigabitEthernet0/0
Once Computer-A identified B’s mac address and the path to get there, then Computer-A will start sending ping messages.
What is ARP age timer?
Did you notice something called Age (min)in the ARP table?\
Every arp entry will have its AGE, once the Age time gets timed out the Arp entry will be removed from its table. you can alter this Age time in the cisco router by entering the command arp timeout on the interface level.
Router(config-if)#arp tim Router(config-if)#arp timeout ? <0-2147483> Seconds Router(config-if)#arp timeout